An exceptionally made sure about the system that intently directs and confines new gadgets, clients, or online traffic streams might be attractive in a cryptic government organization or an organization enviously guarding its licensed innovation and procedure, however it might have less rhyme or reason on the grounds of advanced education establishments, which draw scholarly food from the customary appearances of new individuals from everywhere throughout the world, conveying their own gadgets, hoping to consider and team up nearby every other person.
On the off chance that you run a school or college you don’t really try to figure out a domain that strengthens your picked “insiders” and their information, and keeps out every other person, and their possibly tainted PCs and cell phones. Simultaneously, you despite everything need to secure the individual data and protected innovation of your staff and understudies and ensure that their figuring assets are not being exploited, or used to assault or penetrate different targets. In this way, on those equivalent grounds where the Internet was conceived, executives, scholastics, data innovation staff, and understudies are battling to make sense of the correct method to adjust their scholarly examination and instructive missions with the requirement for PC security.
Research by a dissertation writing service shows that a few schools have not been fortunate with regards to data security. Be that as it may, in different ways, grounds systems bring to mind those having a place with cafés or inns instead of companies. For one, universities, for the most part, have moderately little command over the gadgets that understudies and workforce use nearby. Colleges frequently welcome guests from all finished, who come bearing gadgets of their own and hoping to have the option to associate them. Also, past simply playing host to outside guests, an expanding number of U.S. schools are opening or banding together with global grounds and sending their personnel and understudies abroad to study and instruct at these satellite grounds.
Rather, a few college delegates stated, they attempt to section and parcel their grounds arrangements however much as could be expected so the most touchy, regulatory data can be secured enough while as yet taking into consideration moderately open pieces of the system to help instruct and research plans. However, given how decentralized grounds can be, with singular offices and examination bunches frequently dealing with their own information and assets, it’s not generally direct for a college to monitor where the entirety of its most delicate information is put away and what’s happening overall pieces of its system.
There are two ways of thinking on PC security at foundations of advanced education. One is that colleges are lingering behind organizations in their security endeavors and need to grasp a more secure, corporate way to deal with security. Different holds that organizations are, indeed, coming around to the scholastic foundations’ viewpoint on security—with representatives carrying their own gadgets to work, and an expanding accentuation on checking system movement as opposed to upholding security by attempting to keep out the outside world. For example, some hold up scholastic foundations as models for managing the security dangers presented by bringing your own gadget conditions.
Read More: Challenges, Opportunities and Growth of Cloud Computing in 2020
IT groups answerable for organized security in Universities, Colleges and Schools are encountering increasingly more strain to make sure about their systems from both outer and insider dangers. As indicated by the CSO, 13% of information breaks a year ago occurred at instructive organizations. As per EDUCAUSE, a not-for-profit relationship of IT pioneers in advanced education, data security remains the #1 issue in 2018 for the third year straight. Considering the measure of both individual and budgetary information that scholastic organizations store, it’s maybe to be expected that they’re the objective of the vindictive movement. The scholastic condition is frequently harder to make sure about than in regular organizations or associations. The conventional culture of instruction advances the free trade of thoughts and moment data to benefit the scholastic crucial objectives of any instructive organization.
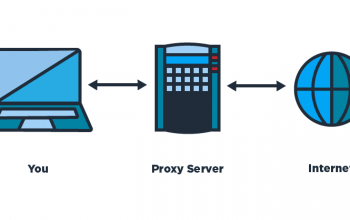
IT groups must locate a suitable method to adjust these entrance esteems that characterize training while ensuring and shielding information and data frameworks. Finding some kind of harmony between an open yet secure system stays a test for all college, school and school IT divisions. These difficulties have prompted some stunning information to penetrate. The tradeoff of more than 600,000 understudy records at the University of Nebraska (the government managed savings numbers, addresses, grades, monetary guide) was maybe the most announced occurrence a year ago and was the consequence of an insider assault – a client working inside the firewall. The most ideal route for colleges to deal with such system breaks is to execute an all-around considered arrangement of the system to control and characterize the executives.
In spite of the training and expanded mindfulness, understudies keep on sharing certifications as there is no result on their own entrance to the system. Genuine security defects can be halted by forestalling synchronous meetings and restricting understudies to just a single potential Windows association at any one example. This stops maverick clients consistently utilizing substantial qualifications simultaneously as the genuine proprietor. Forestalling concurrent logins additionally makes real clients responsible for any ill-conceived move they make – regardless of whether that may be understudy tricks or progressively genuine insider assaults. It guarantees access to the establishment’s basic resources ascribed to one individual maintaining a strategic distance from circumstances concerning responsibility and non-revocation. Strategies and systems would then be able to be reliably upheld to address infringement that does happen.
Read More: Top Gaming Computers That Can Provide Best Gaming Experience
Personnel, staff, and understudies ought to be provisioned distinctively onto the system so the degree of access allowed is fitting for every individual’s job inside the scholastic establishment. Besides visiting educators, instructors and understudies ought to be provisioned independently to guarantee their entrance is stopped upon their flight. Controlling client logins as indicated by client, client gathering or authoritative units are the main lines of resistance for a Windows arrangement and login rights should (and can) be conceded depending on the job of the client inside the association. Such limitations ought to likewise consider other models, for example, workstation or gadget time, working hours and meeting type.